Custom Applications and laaS Trends 2017
By Skyhigh
“Enterprises rely on custom applications to perform business-critical functions. Any downtime could halt operations. Our survey found that while enterprises have confidence in the security of IaaS providers’ underlying infrastructure compared with their own datacenters, data in custom applications is exposed to a wide range of threats independent of the platform. That includes accounts compromised by third parties—via phishing or another method. There are a growing number of examples such as Code Spaces where attackers have held data ransom and in some cases permanently deleted enterprise data in these applications. This report summarizes the scale of custom applications deployed today, where they are deployed, how they are secured, and who is responsible for securing them.”
Tags
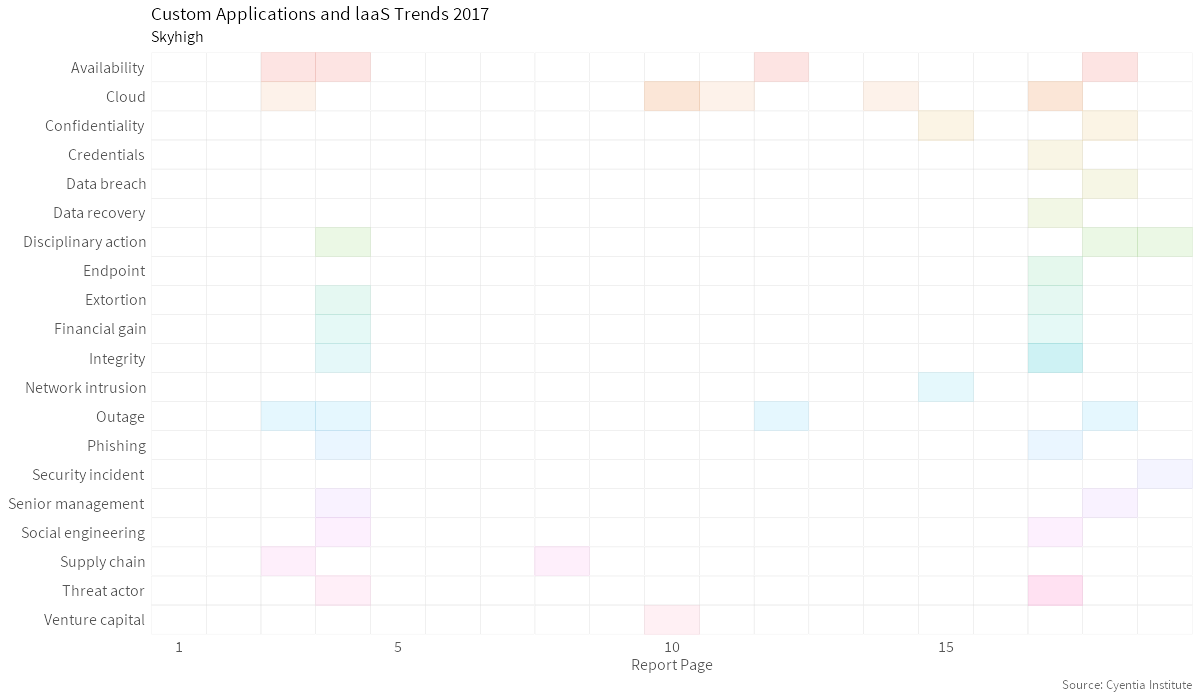
Availability Cloud Outage Disciplinary Action Integrity Threat Actor Confidentiality Extortion Financial Gain PhishingTopic Map